Okta Configuration
EnterpriseBacula Enterprise Only
This solution is only available for Bacula Enterprise. For subscription inquiries, please reach out to sales@baculasystems.com.
Okta is a cloud-based Identity and Access Management (IAM) platform that provides authentication, Single Sign-On (SSO), and policy-driven access control for enterprise applications. It supports OpenID Connect and OAuth 2.0 natively, making it suitable for BWeb delegated authentication.
The following steps configure Okta to act as an OIDC identity provider for BWeb.
Application
Create an application in Okta to represent BWeb.
Sign in to the Okta Admin Console: https://login.okta.com/
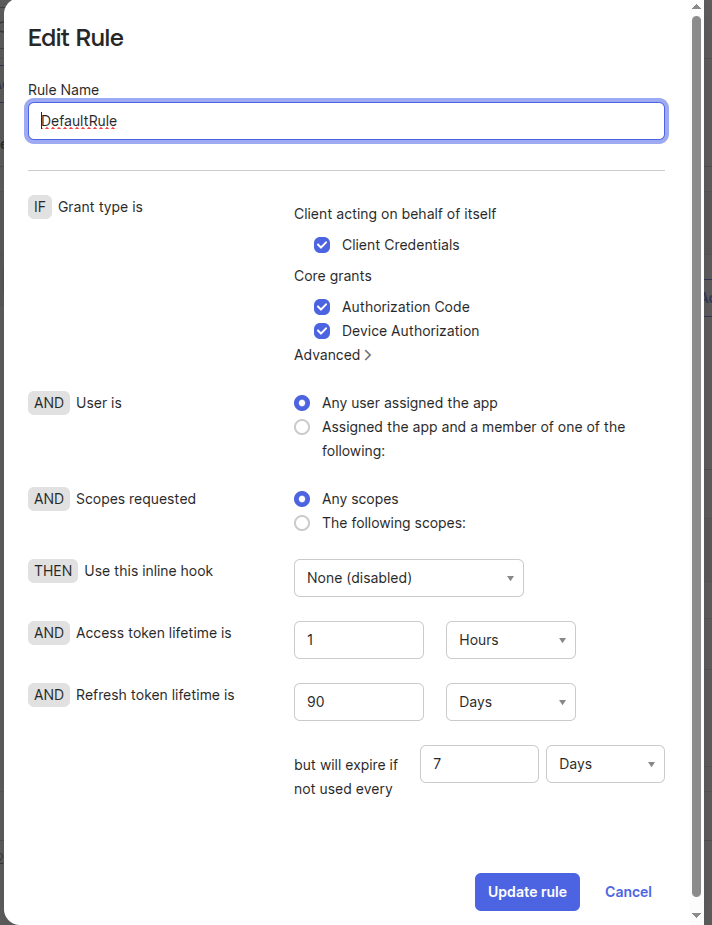
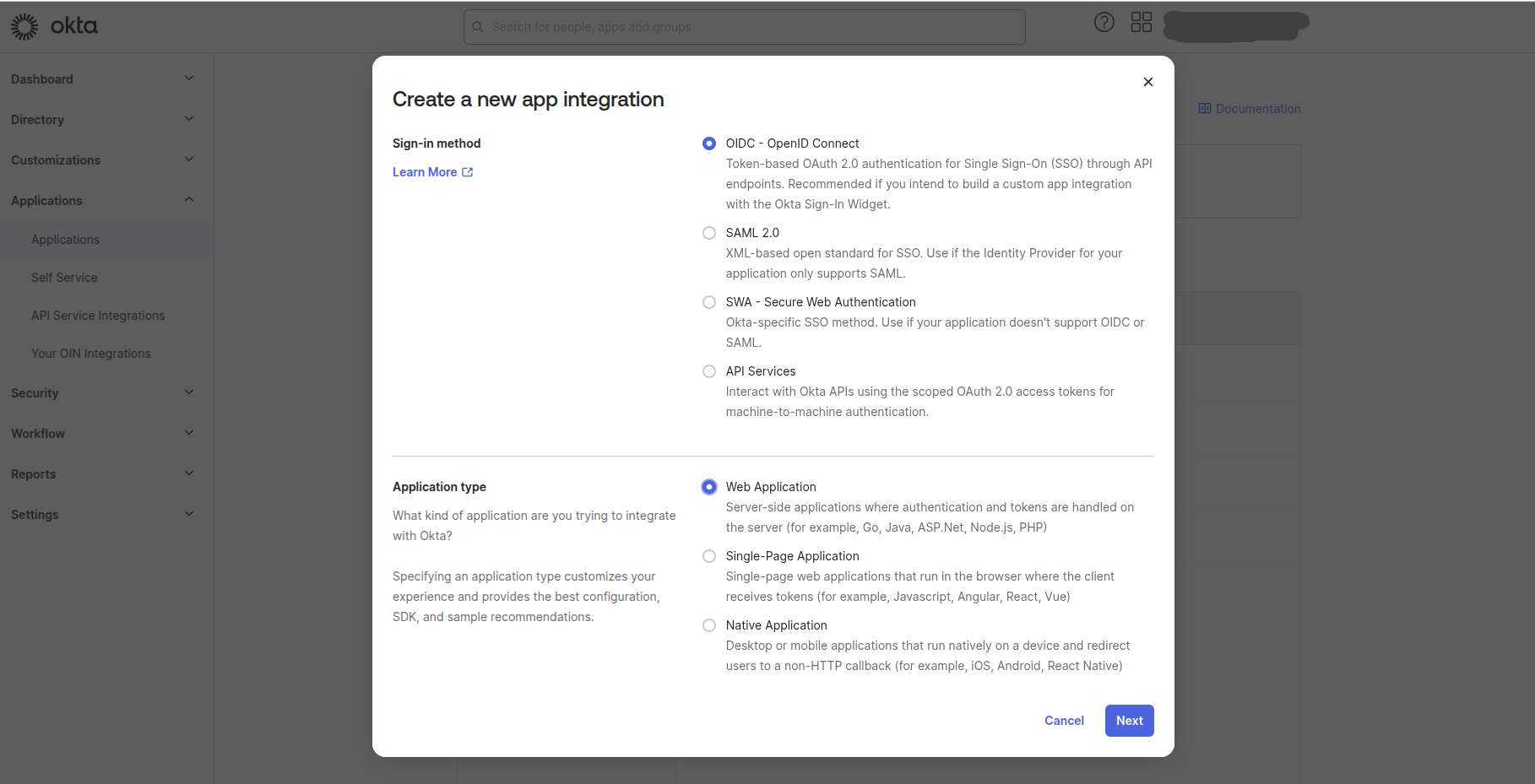
Create a new application and set Sign-in method to OIDC - OpenID Connect and Application type to Web Application.
In the New App Integration form, set at least:
App integration name:
Bacula Enterprise(orBWeb)Grant type:
Authorization CodeSign-in redirect URIs:
https://[bweb.ip.or.hostname]/oauth2/callbackSign-out redirect URIs:
https://[bweb.ip.or.hostname]Login initiated by:
Either Okta or AppLogin flow:
Redirect to app to initiate login (OIDC Compliant)Initiate login URI:
https://[bweb.ip.or.hostname]
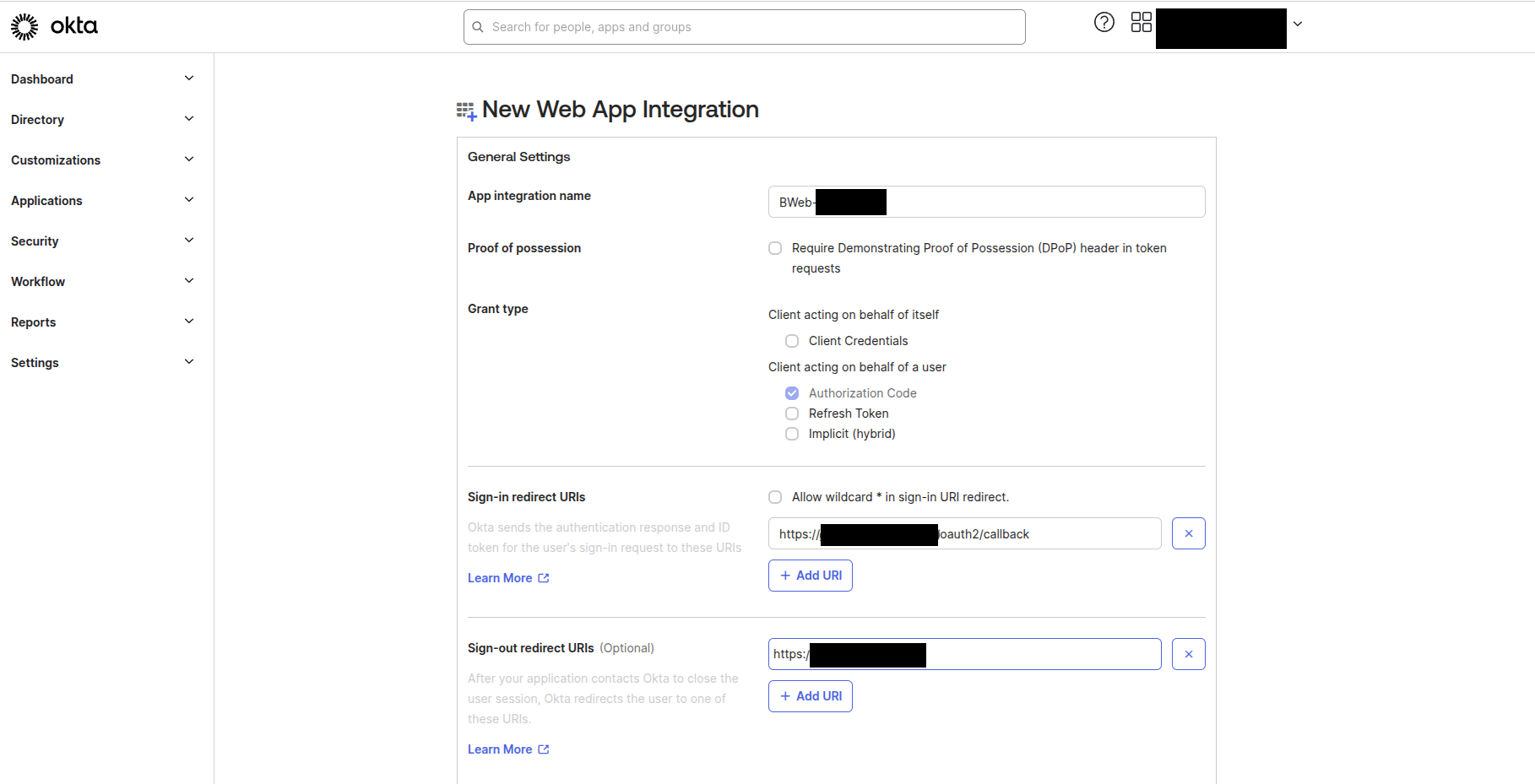
The value [bweb.ip.or.hostname] must be the hostname or IP address used by users to access
BWeb. At this stage, you can select “Skip group assignment for now”.
These URI values must match exactly what users access in browsers, including protocol.
After saving, record the following values for later use:
Client ID (used as
client_id)Client Secret (used as
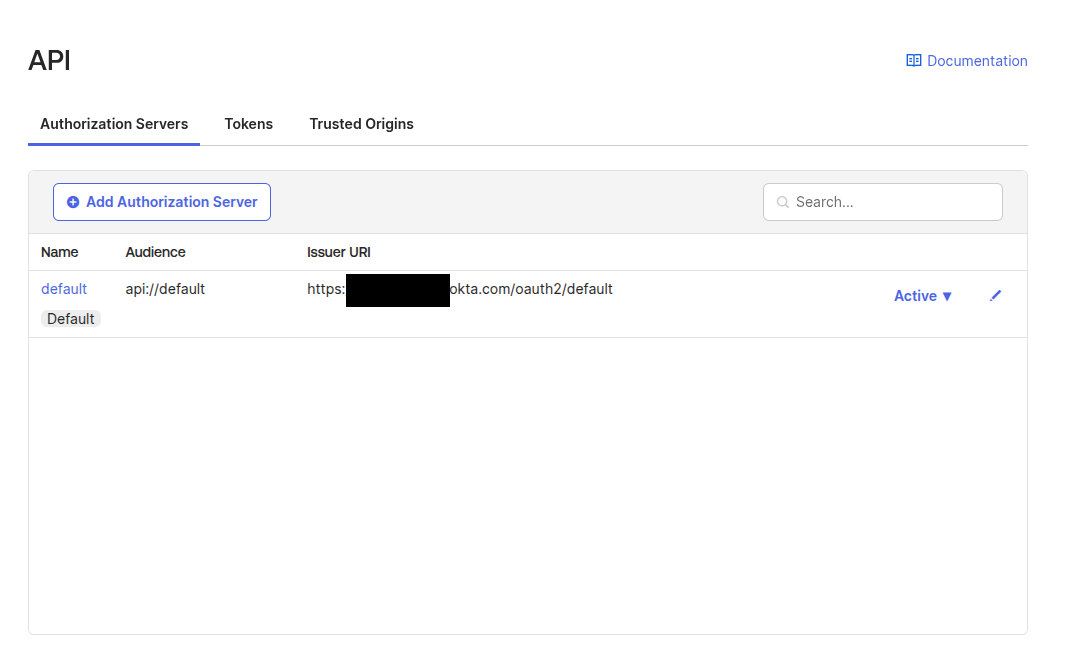
client_secret)Okta issuer URL (typically
https://[your.okta.domain]/oauth2/default)Okta logout URL (typically
https://[your.okta.domain]/login/signout)
Access Group
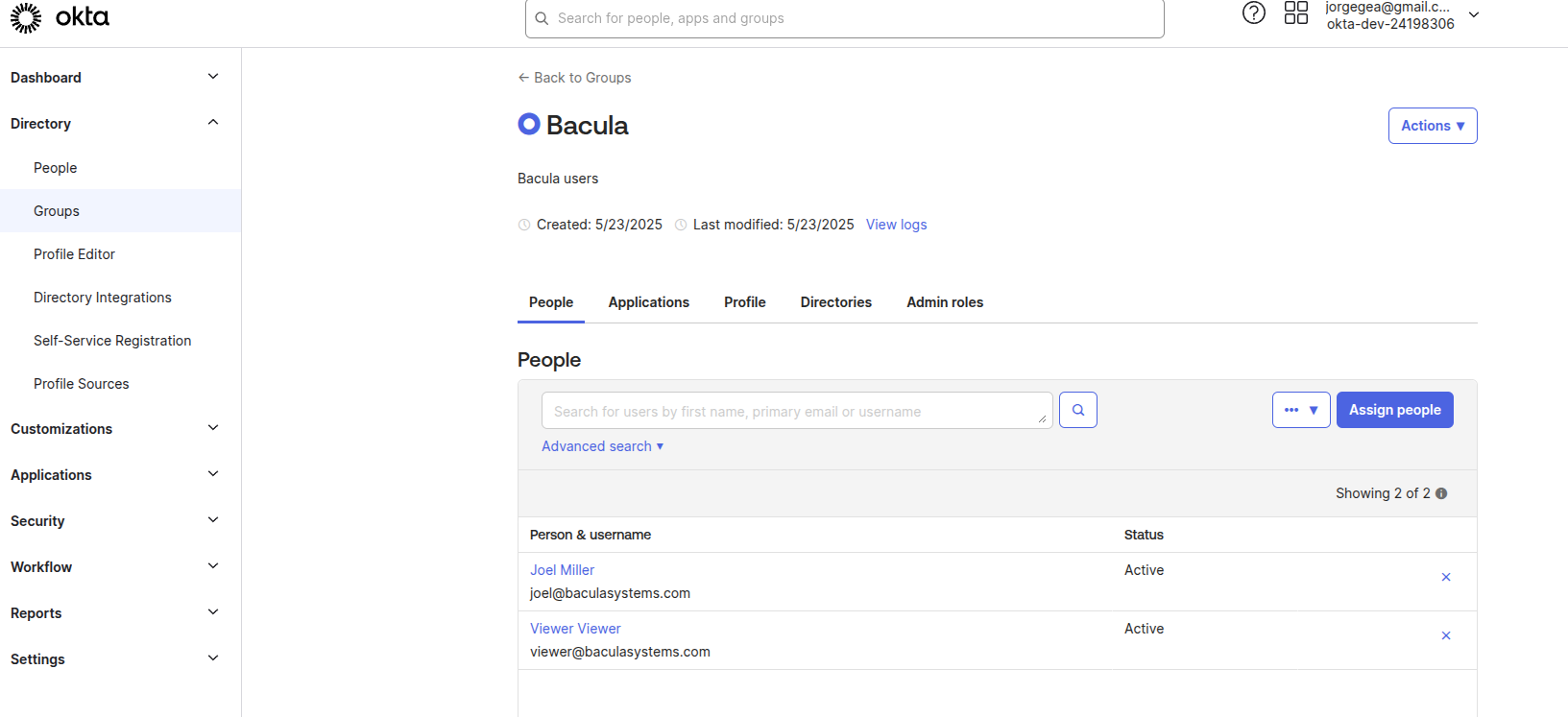
Associate users with the newly created BWeb application. While assignments can be done per-user, it is recommended to use a group.
Create a group (for example,
Bacula).Assign the group to the BWeb application.
Add users to the group.
See also
Previous articles:
Next articles:
Go back to: Authentication via OpenID Connect/OAuth 2.0 and Single Sign-On.